

Categories
Recent Posts
What is Identity Theft & How it Destructs Your Online Presence?
Posted in Cyberbullying by Mike

Identity theft is a cyber offense in which a perpetrator steals your personal information to commit crimes like frauds, scams, deception, and other monetary felonies. Identity theft occurs when someone on the internet misuses your name, house address, photos, social security number, credit card number, passport number, or driving license for financial benefits.
In the worst cases, cybercriminals sell identities and their respective details on the dark web, resulting in serious consequences.
If you know nothing about identity theft or how it destructs your online and physical presence, then continue reading the article to discover more about this dreadful cybercrime.
What is Identity Theft?
Identity theft is the criminal act of stealing personal or financial details to misuse the information. In simpler words, online perpetrators steal someone’s identity. They pretend to be the target in order to use their victim’s credit card, or they misuse the target’s identity to commit serious crimes.
Here are some details about how the perpetrators use data stolen by identity theft:
● Misuse credit card details to open a new line or add credit card numbers on different channels for unauthorized purchases.
● Apply for a tax return to claim the refund.
● Data trade on the dark web.
● Manipulation of employment details to pass background checks or to prove financial standing.
● Pretend to be someone else using photos, ID card details to gain the trust of personal or corporate relations.
● Impersonate the target’s identity for sexual or monetary benefits.
Identity theft crimes are common across the world.
In the year 2020, American businesses experienced 47% of identity theft cases.
Common Identity Theft Approaches:
Several ways can help perpetrators steal the identity of the target person. Online media have provided cybercriminals a vast space to mess around. Not only are personal details at stake, but corporate information is also vulnerable to identity thefts.
Here are some common approaches to identity theft:
Phishing:
Phishing includes the transmission of encrypted malicious software to the computer device of the target person. The malware mines the computer system and fetches all the data cached or stored on it. Then, the recorded personal or financial information is sent to a remote server, from where the perpetrator can access the data. Phishing is commonly done by sending fraudulent emails.
Wi-Fi Hacking:
Cybercriminals can access user data via open Wi-Fi networks. Mostly, public Wi-Fi connections are decrypted. As a result, cybercriminals can hack into public internet connections and snoop information from linked devices. Moreover, perpetrators can create a fake Wi-Fi network to attack vulnerable devices and steal information from them.
Skimming:
Credit/debit card skimming involves the implantation of an imitation system at cash counters to capture data from the card’s magnetic stripe. Sometimes, the perpetrators install a camera to get ZIP codes and ATM pins. Credit or Debit card skimming enables criminals to make fraudulent purchases and transfer money by providing the account holder’s information.
Phone Scams:
Phone scams are getting more common day by day. Con artists make phone calls to people and pretend to represent their bank or insurance company. They then ask for the exclusive details of their bank account or insurance ID information. Unfortunately, people fall for phone scams very quickly and provide delicate information, which results in immense trouble.
Catfishing:
Catfishing is somewhat a cybercrime with more personal benefits. However, people can catfish victims to earn their confidence to ask for private information. Catfishing starts with cyberstalking. However, it can be dreadful. Catfishing perpetrators first learn about their target’s interests and then pretend to be people with similar preferences and habits. The victim starts trusting the felon over time and eventually shares personal details with them without knowing their true intentions.
Data Breaches:
Businesses around the world have experienced data breach issues at some point in their corporate journey. Cyber perpetrators steal corporate information and sell it on the dark web or leak business details to rivals. The majority of data breaches cases have a similar purpose – ransom money. The corporate data breach is a serious crime that can risk business and employee information at stake.
Dumpster Diving:
Dumpster diving is usual in every zone where we dump trash or unuseful things. Well, some smart brains can steal private mails, bills, or other documents to commit an identity theft felony. Information such as bank account numbers, health insurance details, credit card data, allows thieves to create a duplicate identity, or worse if they get the social security number of someone. Dumpster diving only gets successful if people trash out mails or documents unshredded.
Malware:
The easiest way to steal someone’s details is by transferring malicious software, aka malware, to their cell phone or computer. Digital devices now store significant data of users, including bank account information, personal data, photos, documents, and other material. Malware software cracks the security of a digital device and steals all the stored information in secret mode. The user can’t detect if a malicious program is active on the device. Standard malware programs are viruses, spyware, keyloggers, and trojans.
Child ID Theft:
ID theft occurs when a perpetrator steals the social security number of someone’s child in order to apply for government aid, loan, apartment, or to open financial accounts. Child Identity theft can cause serious problems, such as a kid whose ID was stolen won’t know about the criminal activity and will be exposed to loan payments and other stuff in adulthood.
READ ALSO: All About Cyber Dangers Every Parent Should Know
Tax ID Theft:
Perpetrators can apply for tax returns with identity theft. They can misuse the social security number to collect tax refunds. The target won’t know about the tax return application submission until they apply themselves.
Identity theft can risk the future of the target and their associates terribly. That is why it is crucial to protect your digital and printed details before any criminal can exploit and misuse your identity.
How to Secure Your Information from Identity Theft?
Living in a digitalized era, it is impossible to keep away credit card details, health insurance numbers, and other details from digital devices. Businesses run digitally, with all the corporate data stored on cloud storage. In addition, people purchase online products using online payment methods.
Unfortunately, every digital footprint is at risk of cybercrime exposure.
Here are some tips to secure your details from identity theft:
● Generate a unique password for all your digital accounts. Try to use symbols, digits, capitalized letters, and other characters. You can paraphrase your password to make it more secure.
● Enable two-factor authentication on your devices. Password-protected accounts are less vulnerable to data breach attempts.
● Never share your confidential details online or with someone you know. Keep bank account credentials to yourself. Also, keep your social security number secure.
● Always shred documents, including; mails, receipts, bills, vouchers, and other paperwork with your information written before discarding them.
● Prefer paperless billing, so your account details will be protected.
● Avoid taking social security cards, health insurance cards, or debit cards everywhere you go.
● While making an online purchase, make sure the website is secure. Trust websites that have “HTTPS” in the URL.
● Don’t click on unknown links or open unauthorized emails; such content contains malware to fetch all the details saved on the user’s device.
Cyberstalking is one of the main approaches to finding identity theft targets. On the other hand, catfishing can also intimidate people into sharing personal details with the perpetrators.
Final Note:
The online world is immense, and people can easily fetch personal details with data breach attempts. To evade identity theft and other online felonies, we must protect our digital data. For example, businesses can use employee monitoring software to keep their eyes on employees’ online actions. In contrast, parents can use parental control apps to limit their kids’ device usage.
Categories
Recent Posts
Related Posts

How Internet Trolling is Cultivating Culture of Hate?
Trolling has become a headache for internet users. But don’t...
Read More
What is Sharenting? Does It Invite Unsolicited Dangers?
Sometimes parents and social media are inseparable. Parents feel over...
Read More
Online Shaming & Its Terrible Consequences – A Parental Guide
When the internet started booming, everyone rushed to grab the...
Read More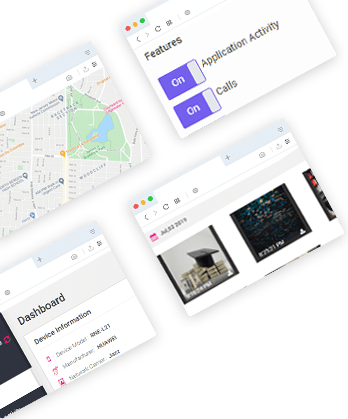

Install TheWiSpy Monitor App Now and Start Exploring Your Kid’s and Employee’s Digital Space
- Protect Your Kids
- Secure Your Business
- Backup Personal Data
- Products
- Features
- Social Media Monitoring
- Web Browsers HistoryNew
- Call Recording
- Track Call History
- Hack Phone Contacts
- Monitor Saved Photos
- Spy Microphone Surroundings
- App Monitoring
- Spy Text Messages
- Video Recording
- Voice Message Recording
- Wifi Log
- Spy Camera
- Remote Access to Target Phone
- 24/7 Instant Alerts
- GPS Location
- Pricing
- Blog
- Help
- +1 808-278-9881
- Demo
 Affiliate Login
Affiliate Login- Affiliate Registration
 Login
Login- Sign Up
 English
English Spanish
Spanish
 Spanish
Spanish